-
Address
52, Achasan-ro 15-gil, Seongdong-gu,
Seoul, Republic of Korea
(Samhwan Digital Venture Tower 2nd floor) - Tel
- Fax
- Download
Technology Comparison
Post-QuanOtum
Post-QuanOtum
Cryptography
Post-Quantum Cryptography
PQC is
highly compatible.
and has a technology that can be used universally
without any concern about performance degradation.
Post-Quantum

Types of
Post-quantum
cryptography technology
-
 QKD
QKDQuantum Key
Distribution -
 PQC
PQCPost-Quantum
Cryptography -
 Hybrid PQC
Hybrid PQCHybrid Post-Quantum
Cryptography
Difference between QKD and PQC
| QKD Quantum Key Distribution | PQC* Post-Quantum Cryptography | |
|---|---|---|
| Characteristic | Quantum mechanics ensure that quantum channels cannot be successfully intercepted without detection |
100% guarantee that no way to break the PQC algorithm can be found |
| Security | Special hardware required | Most implementations are software-only, No special hardware required |
| Implementation | Fiber Optics or free space optics that only work in fiber optics |
Applied to all types digital communication media including RF, wired network, and optical communication |
| Cost | Relatively high cost due to the need for hardware and new communication infrastructure |
Relatively low cost based on software |
| Repeater Compatibility |
A repeater can receive a quantum channel, decode it into classic bits, and re-encrypt and retransmit it to another quantum channel. |
Fully compatible with current digital repeater technology |
| Mobile device compatibility |
Very limited For line-of-sight nodes only |
Compatible with all types of communication used on mobile |
| Digital Signature Compatibility |
Potentially used for digital signatures |
Developing various standards for digital signature applications |
Features of PQC and Hybrid PQC
PQC Features
It completely replaces the existing method, but it is less general and there is a risk of performance degradation.
| 3 ROUNDS | ||
|---|---|---|
| PUBLIC KEY ENCRYPTION | ALGORITHM | CLASSIFICATION |
| CLASSIC MCELIECE | ENCRYPTION-BASED ENCRYPTION | |
| CRYSTALS KYBER | LWE | |
| NTRU | NTRU | |
| SABER | LWR | |
| DIGITAL SIGNATURE | CRYSTALS-DILITHIUM | LWE |
| FALCON | NTRU | |
| RAINBOW | MULTIVARIATE | |
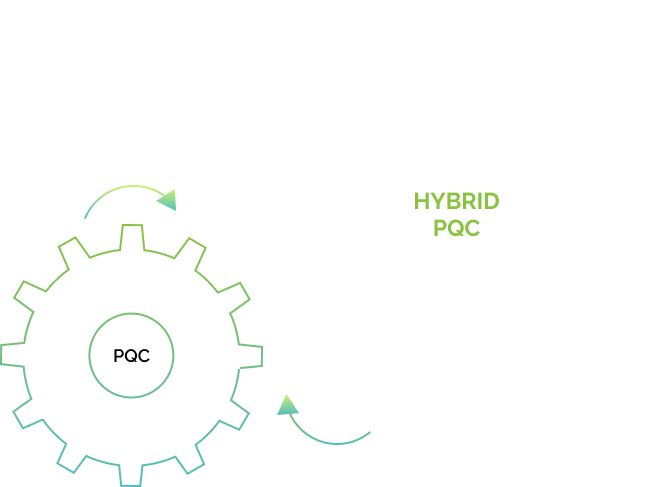
Hybrid PQC Features
With optional application, it can be applied without concern of performance degradation and can be used more universally.
-
 Choose either the existing key exchange method or PQC method.
Choose either the existing key exchange method or PQC method.
After combining it with the XOR calculation, the final secret key can be
generated and used. -
 PQC algorithm can be selectively applied to the TLS method being
PQC algorithm can be selectively applied to the TLS method being
currently in use



